How to properly store encryption key images are ready. How to properly store encryption key are a topic that is being searched for and liked by netizens now. You can Download the How to properly store encryption key files here. Find and Download all royalty-free vectors.
If you’re looking for how to properly store encryption key images information connected with to the how to properly store encryption key keyword, you have come to the right blog. Our website always provides you with hints for seeking the maximum quality video and picture content, please kindly hunt and locate more informative video content and graphics that match your interests.
How to safely store encryption key in a NET assembly. I know this is not ideal and am now building a web app that will store medical data so I want to do it as best as would be reasonably expected. You have to decide what is an acceptable level of risk. How to properly store an encryption key. - If you can apply meaningful ACLs to the file that stores the value then do so.
How To Properly Store Encryption Key. Websites have SSLTLS certificates containing the public key while the private key is installed on the websites origin server or CA. 15022019 You can store your private keys in a cryptomator secured directory and have it encrypted in real time with your cloud provider. When you start a SQL Server instance the SQL Server database calls the EKM Provider software to. How to convert DateTime to Unix timestamp and vice versa in C.
 Classtools Net Arcade Game Generator Coding Key Storage Qr Code From pinterest.com
Classtools Net Arcade Game Generator Coding Key Storage Qr Code From pinterest.com
The key rotation period should depend on your needs. 25072019 To decrypt data all you need to do is take the encrypted message and break it into two pieces. 06062017 With your constraints there is no way to safely store keys and this is from a hardware perspective. These approaches are platform-agnostic. How to get the Cartesian product of a series of lists. 05042009 That way you dont have to store the key or at least any keys whether they are symmetric or private keys can be encrypted with this bootstrap.
Websites have SSLTLS certificates containing the public key while the private key is installed on the websites origin server or CA.
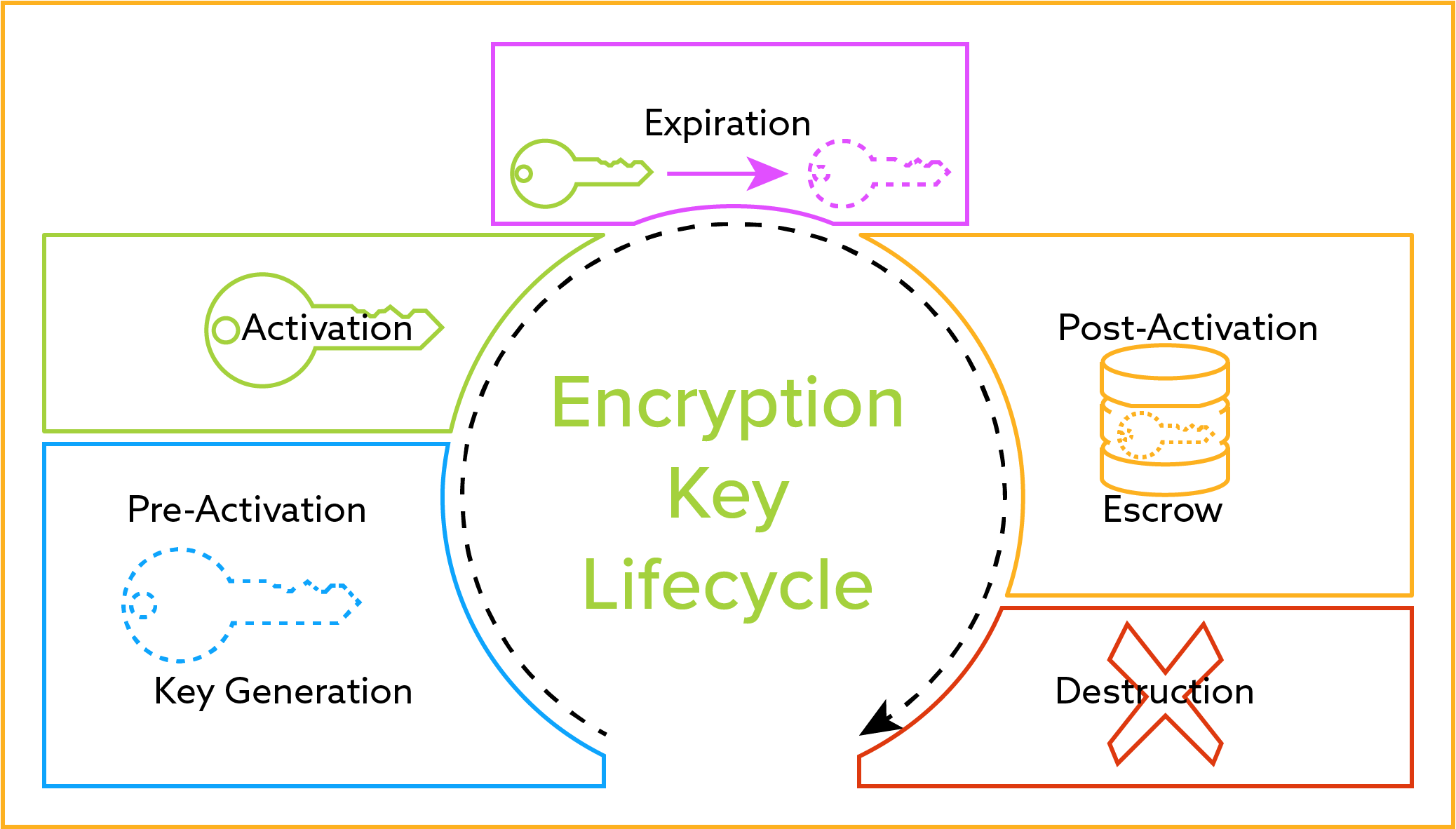
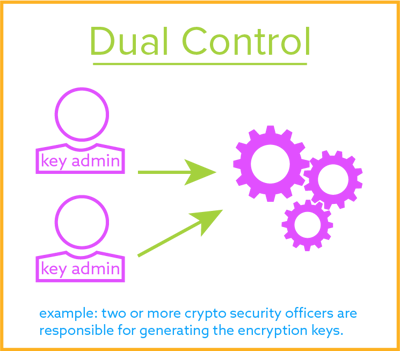
The key can be created by a sole administrator or through dual control by two administrators. It would have cost less than a penny to add a hardware core if you had a custom IC. Check key existing get position of key and value get key by value in a dictionary in Python. The encryption key is created and stored on the key management server. 25072019 To decrypt data all you need to do is take the encrypted message and break it into two pieces. I have done a bit of encryption of data in the past and just stored my encryption key in applicationcfc.
 Source: docs.mongodb.com
Source: docs.mongodb.com
Finally you decrypt the encrypted data using the data key that you just decrypted. 15022019 You can store your private keys in a cryptomator secured directory and have it encrypted in real time with your cloud provider. How to get the Cartesian product of a series of lists. Grant read permissions only to the group of users that are allowed to use the password. The key manager creates the encryption key through the use of a cryptographically secure random bit generator and stores the key along with all its attributes into the key storage database.
 Source: info.townsendsecurity.com
Source: info.townsendsecurity.com
- Used the ProtectedData class to encrypt the value as stored on disk. How to convert DateTime to Unix timestamp and vice versa in C. 07052019 You would need to provide the password to your web server every time you start it since it isnt stored anywhere. If not store your secret key in a file by itself and modify its permissions to make it accessible only to the user running the web application. 05042009 That way you dont have to store the key or at least any keys whether they are symmetric or private keys can be encrypted with this bootstrap.
 Source: documentation.suse.com
Source: documentation.suse.com
How to sort a list of dictionaries by a value of the dictionary. Grant read permissions only to the group of users that are allowed to use the password. 07052019 You would need to provide the password to your web server every time you start it since it isnt stored anywhere. The key manager creates the encryption key through the use of a cryptographically secure random bit generator and stores the key along with all its attributes into the key storage database. How to sort a list of dictionaries by a value of the dictionary.
 Source: b-vieira.medium.com
Source: b-vieira.medium.com
Finally you decrypt the encrypted data using the data key that you just decrypted. You then ask AWS to decrypt the encrypted data key using the master key AWS maintains this gives you the original data key. 05082018 Expecting the compromise of E it would be a good idea to periodically rotate keys and move old keys away from E to safe offline storage so any incident wont affect files encrypted with previous keys. 30092019 The encrypted database key is then stored locally on disk in the SQL Server context. The key rotation period should depend on your needs.
 Source: info.townsendsecurity.com
Source: info.townsendsecurity.com
How to read inputs as numbers. There is no safe. The key rotation period should depend on your needs. You have to decide what is an acceptable level of risk. If you have a way to update the firmware I can get something in there to get the keys out.
 Source: thesslstore.com
Source: thesslstore.com
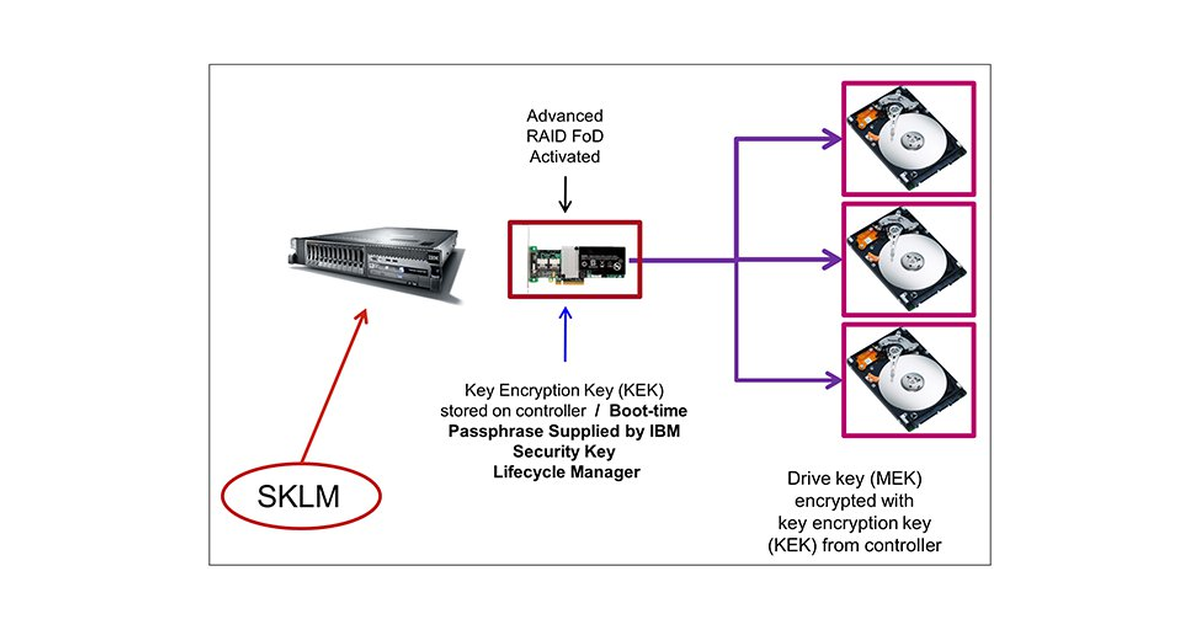
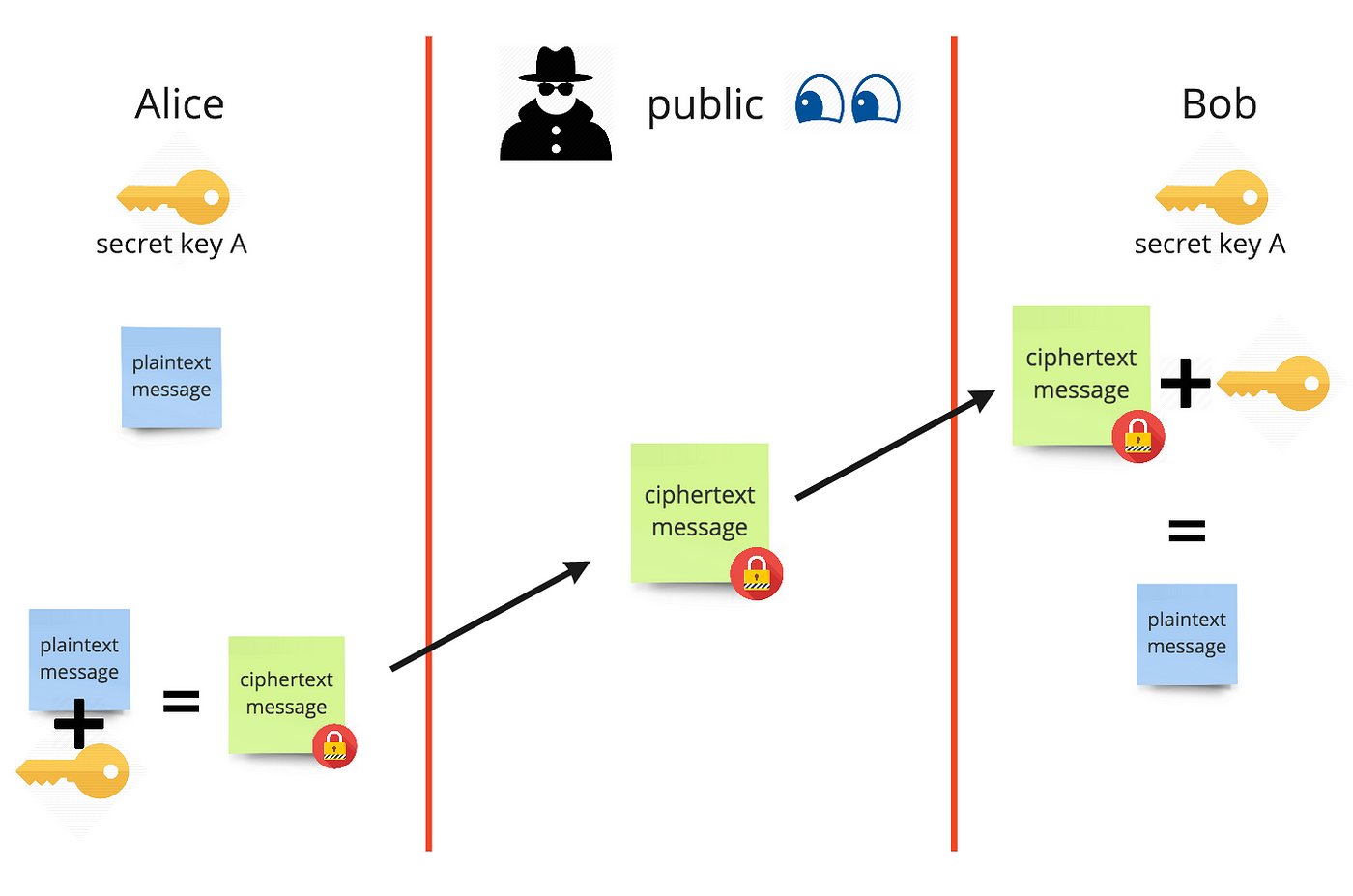
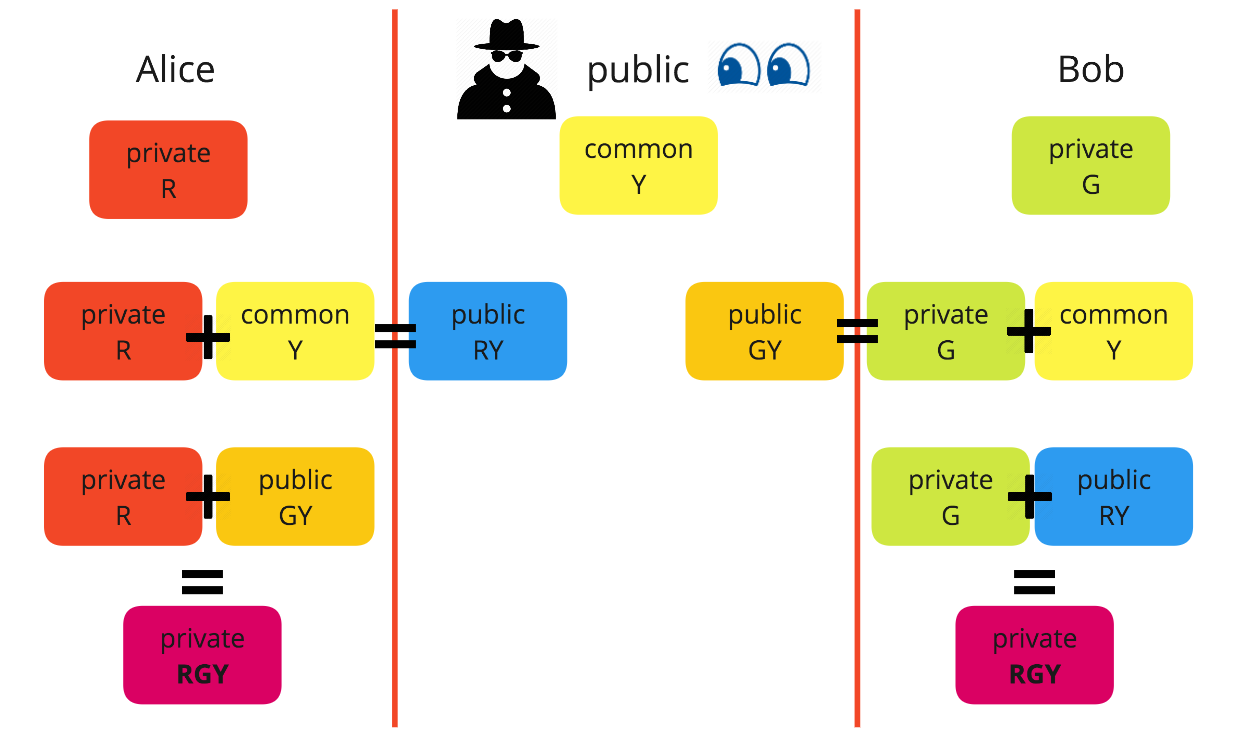
25072019 To decrypt data all you need to do is take the encrypted message and break it into two pieces. Websites have SSLTLS certificates containing the public key while the private key is installed on the websites origin server or CA. First the encryption key is created and stored on the key management server which can be a hardware security module HSM virtual environment VMware or a true cloud instance. I know this is not ideal and am now building a web app that will store medical data so I want to do it as best as would be reasonably expected. Public key cryptography is vital for Secure Sockets Layer SSL and Transport Layer Security TLS which are themselves vital for secure HTTPS web browsing.
 Source: pinterest.com
Source: pinterest.com
23072020 How SSLTLS Uses Public Key Encryption. 30092019 The encrypted database key is then stored locally on disk in the SQL Server context. The key rotation period should depend on your needs. Probably the best thing you can do is this. If the risk of someone using reflector or just opening up the assembly using the SystemReflectionAssembly class and.
 Source: lenovopress.com
Source: lenovopress.com
You have to decide what is an acceptable level of risk. 10112008 Slightly better I think to store it in the filesystem. It would have cost less than a penny to add a hardware core if you had a custom IC. 05042009 That way you dont have to store the key or at least any keys whether they are symmetric or private keys can be encrypted with this bootstrap. - Used the ProtectedData class to encrypt the value as stored on disk.
 Source: medium.com
Source: medium.com
20082014 Otherwise it would be easy to find all the common data in a database and deduce a pattern from the encryption. How to sort a list of dictionaries by a value of the dictionary. How to properly store an encryption key. 05082018 Expecting the compromise of E it would be a good idea to periodically rotate keys and move old keys away from E to safe offline storage so any incident wont affect files encrypted with previous keys. Check key existing get position of key and value get key by value in a dictionary in Python.
 Source: medium.com
Source: medium.com
25072019 To decrypt data all you need to do is take the encrypted message and break it into two pieces. 23072020 How SSLTLS Uses Public Key Encryption. 05042009 That way you dont have to store the key or at least any keys whether they are symmetric or private keys can be encrypted with this bootstrap. A cryptocurrency wallet is a software program designed to store your public and private keys send and receive digital currencies monitor their balance and interact with various blockchains. - If you can apply meaningful ACLs to the file that stores the value then do so.
 Source: docs.mongodb.com
Source: docs.mongodb.com
The key manager creates the encryption key through the use of a cryptographically secure random bit generator and stores the key along with all its attributes into the key storage database. 30092019 The encrypted database key is then stored locally on disk in the SQL Server context. How to get the Cartesian product of a series of lists. First the encryption key is created and stored on the key management server which can be a hardware security module HSM virtual environment VMware or a true cloud instance. Finally you decrypt the encrypted data using the data key that you just decrypted.
This site is an open community for users to submit their favorite wallpapers on the internet, all images or pictures in this website are for personal wallpaper use only, it is stricly prohibited to use this wallpaper for commercial purposes, if you are the author and find this image is shared without your permission, please kindly raise a DMCA report to Us.
If you find this site serviceableness, please support us by sharing this posts to your favorite social media accounts like Facebook, Instagram and so on or you can also save this blog page with the title how to properly store encryption key by using Ctrl + D for devices a laptop with a Windows operating system or Command + D for laptops with an Apple operating system. If you use a smartphone, you can also use the drawer menu of the browser you are using. Whether it’s a Windows, Mac, iOS or Android operating system, you will still be able to bookmark this website.